If you will be leveraging a Hardware Load Balancer for your Exchange 2010 environment there are some additional Exchange specific setting modification required to get this working, whether you are using PassThrough, SSLOffloading or ReverseSSL (aka SSLBridging).
-
System Requirements for this configuration: EXCHANGE SERVER 2010 “SP1”
Options for Load Balancing Exchange 2010 CAS Servers using Hardware Load Balancer:
-
Pass Through
- Simple and a very common deployment method
- Configuration Requirements
- Set MSExchangeAB and MSExchangeRPC static ports (AB and RPC should be set to different port numbers.
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MSExchangeAB\Parameters]
"RpcTcpPort"="60001"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MSExchangeRPC\ParametersSystem]
"TCP/IP Port"=dword:0000ea60 -
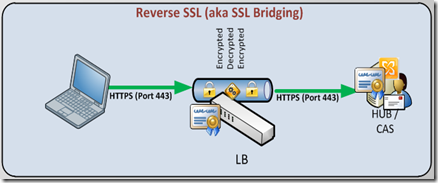
Reverse SSL (aka SSL Bridging) --- Recommended
- More advanced configuration, and more advanced forms of loadbalancing available.
- Benefits:
- Secure communications end-to-end; no passwords in clear text between HLB and CAS
- Less configuration required on Exchange 2010 than SSLOffloading below.
- If your Exchange 2010 CAS are already configured, the only configuration remaining is Set MSExchangeAB and MSExchangeRPC static ports (AB and RPC should be set to different port numbers.
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MSExchangeAB\Parameters]
"RpcTcpPort"="60001"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MSExchangeRPC\ParametersSystem]
"TCP/IP Port"=dword:0000ea60 - Disadvantages:
- Does not offload (encryption and decryption) cpu processing from the CAS Servers.
-
SSLOffloading
(Note the script as the end of this article will configure all of these parameters for you)
- More advanced forms of loadbalancing available. (This Article provides steps to configure)
- Configuration Requirements
- Set MSExchangeAB and MSExchangeRPC static ports (AB and RPC should be set to different port numbers.
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MSExchangeAB\Parameters]
"RpcTcpPort"="60001"
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\MSExchangeRPC\ParametersSystem]
"TCP/IP Port"=dword:0000ea60 - Remove “Require SSL from Default Website and All Exchange Virtual Directories on each CAS Server
- Enable Outlook Anywhere, Set Authentication Basic and Set Outlook Anywhere SSLOffloading to TRUE
- Set OWA for SSLOffloading
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Services\MSExchange OWA' -Name SSLOffloaded -Value 1 -PropertyType DWORD - Modify the web.config file for Autodiscover and EWS
# Configure web.config files
$path = (Get-AutodiscoverVirtualDirectory -Server ($env:COMPUTERNAME)).Path
(Get-Content $path\web.config)| Foreach-Object {$_ -replace "httpsTransport", "httpTransport"} | Set-Content $path\web.config
$path = (Get-WebServicesVirtualDirectory -Server ($env:COMPUTERNAME)).Path
(Get-Content $path\web.config)| Foreach-Object {$_ -replace "httpsTransport", "httpTransport"}| Set-Content $path\web.config
Important
If you configure SSL offloading on an Exchange 2010 CAS server, all user passwords will be sent in clear between the HLB device(s) and the CAS servers, so it's important the traffic is sent over a secure network not accessible by malicious users. If the security policy within the organization states that all passwords should be sent in an encrypted form (even when occurring over a secure network), it's recommended to enable reverse SSL on the HLB device(s). In addition, it's recommended to enable reverse SSL, if the organization does not have a secure network in place between the HLB device(s) and the CAS servers or if there's no noticeable performance gain of offloading SSL to the HLB device(s) in the environment.
SCRIPT to Configure CAS for SSLOffloading
#This script will configure the Exchange 2010 Client Access Servers
# for Hardware loadBalancer with SSLOffloading enabled.
#
# System Requirements: EXCHANGE SERVER 2010 "SP1"
#
#
# Set registry key
.
"$($env:windir)\system32\inetsrv\appcmd" set config "Default Web Site/Autodiscover" -commitPath:APPHOST -section:access -sslFlags:None.
"$($env:windir)\system32\inetsrv\appcmd" set config "Default Web Site/ecp" -commitPath:APPHOST -section:access -sslFlags:None.
"$($env:windir)\system32\inetsrv\appcmd" set config "Default Web Site/EWS" -commitPath:APPHOST -section:access -sslFlags:None.
"$($env:windir)\system32\inetsrv\appcmd" set config "Default Web Site/Microsoft-Server-ActiveSync" -commitPath:APPHOST -section:access -sslFlags:None.
"$($env:windir)\system32\inetsrv\appcmd" set config "Default Web Site/owa" -commitPath:APPHOST -section:access -sslFlags:None.
"$($env:windir)\system32\inetsrv\appcmd" set config "Default Web Site/rpc" -commitPath:APPHOST -section:access -sslFlags:None# Configure web.config files $path = (Get-AutodiscoverVirtualDirectory -Server ($env:COMPUTERNAME)).Path
(
Get-Content $path\web.config)| Foreach-Object {$_ -replace "httpsTransport", "httpTransport"} | Set-Content $path\web.config $path = (Get-WebServicesVirtualDirectory -Server ($env:COMPUTERNAME)).Path(
Get-Content $path\web.config)| Foreach-Object {$_ -replace "httpsTransport", "httpTransport"}| Set-Content $path\web.config # Configure Outlook Anywhere $enabled = Get-OutlookAnywhere –Identity "$($env:COMPUTERNAME)\RPC*" If ($enabled){Set-OutlookAnywhere –Identity
"$($env:COMPUTERNAME)\RPC*" -SSLOffloading $true} Else{
Write-Host "Configure Outlook Anywhere and remember to check the box to enable SSL Offloading"} Write-Host -f Red "NOTE: Run `"iisreset /noforce`" to complete the process"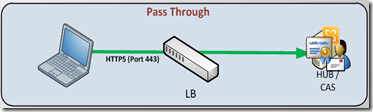

No comments:
Post a Comment